Why We Invested in Spectrum

Detection was built for a human-speed world. That world is over.
We'd been waiting for this company before we knew it existed.
For years at TechOperators, we watched the cybersecurity industry pour money into everything that happens after a threat is detected. Faster triage. Smarter orchestration. Automated response. Better dashboards for the alerts analysts were already drowning in. Hundreds of millions in venture capital flowing toward the same thesis: if we can just respond faster, we win.
Now the industry is doing it again with AI. A wave of AI-powered SOC platforms promising to triage alerts faster, investigate smarter, and automate response at machine speed. But faster triage on a broken detection foundation doesn't solve the problem. It scales it. If the detections are wrong — if they're incomplete, silently broken, or missing the threats that actually matter — then all the AI triage in the world just gives you faster, more confident wrong answers.
Nobody seemed to be going upstream. Nobody was asking the harder question: before you build the AI SOC, shouldn't you fix what feeds it?
The first time Meny Har walked me through what Spectrum Security was building, we were finishing each other's sentences. Not because I'd been briefed. Because I'd lived the problem he was describing — the detection layer, the logic that determines whether a security program sees the threat or doesn't. The part of the stack everyone depends on and nobody has modernized. The part that's still done by hand.
TechOperators is leading Spectrum's $19M Seed, alongside Whiterabbit Ventures, Skinos Ventures (a new cybersecurity fund by Shlomo Kramer and Yishay Yovel), and Alumni Ventures. I'm joining the board. This is the investment that felt the most inevitable.
The Layer That Makes Security See
Every enterprise on Earth runs security tooling that ingests billions of events a day — SIEMs, data lakes, cloud platforms, endpoint agents. But raw telemetry is just data. To turn it into security alerts, someone has to write detection logic: rules that define what suspicious behavior looks like in your specific environment, against your specific infrastructure, for your specific threat profile. The people who write those rules are detection engineers. Without their work, your entire security investment is an expensive storage bill. Organizations pour millions into security infrastructure — tools, teams, threat intelligence, red teams, compliance programs — and after all that spend, most still cannot confidently answer the most basic question: can we actually detect the threats targeting us right now?
Anyone who has run a SOC knows the truth: most organizations have massive gaps in their detection coverage, rules that silently break and drift, and nowhere near enough people to keep up. Detection engineering is still almost entirely manual, and the backlog never shrinks. It compounds.
That was a hard problem when attackers operated at human speed. It is now an impossible one.
Eighteen months ago, an attacker who wanted to exploit a new vulnerability needed skill, time, and luck. Today, an AI agent can take a published advisory, generate a working exploit chain, adapt it to a target environment, and launch a campaign — continuously, autonomously, and at near-zero marginal cost. The iteration loop that used to take weeks now takes hours. And it's compressing.
The defense hasn't kept up. It hasn't even come close. Everyone paying attention knows it — CISOs are already reprioritizing detection engineering from an afterthought to the most critical function in the stack. The question is what to do about it.
The New Detection Fabric
Spectrum is building the detection fabric for this new reality. Their platform automates the full detection lifecycle — threat ingestion, environmental analysis, detection authoring, testing, deployment, health monitoring, and drift remediation — across a customer's existing security stack. No rip-and-replace. It layers intelligence on top of the tools teams already run, and it works wherever detection logic needs to live.
Security teams stay in control — setting priorities, validating what ships, maintaining oversight of what runs in production, with full transparency into how each detection was generated and why. In customer environments, Spectrum has compressed detection authoring from 121 days to under 30 minutes. Engineering hours reduced by 90%. Authoring accuracy improved by 75%. A customer described the output as performing at the level of a senior detection engineer on their team — on live enterprise workloads, not a demo.
For the first time, the speed of the defense can match the speed of the attack. And this is just the beginning — Spectrum is building toward a world where detection is fully autonomous, continuously adapting, operating at machine speed against threats that never stop evolving.
Built for This Moment
But the technology alone isn't what convinced me. It's who built it and who's around it.
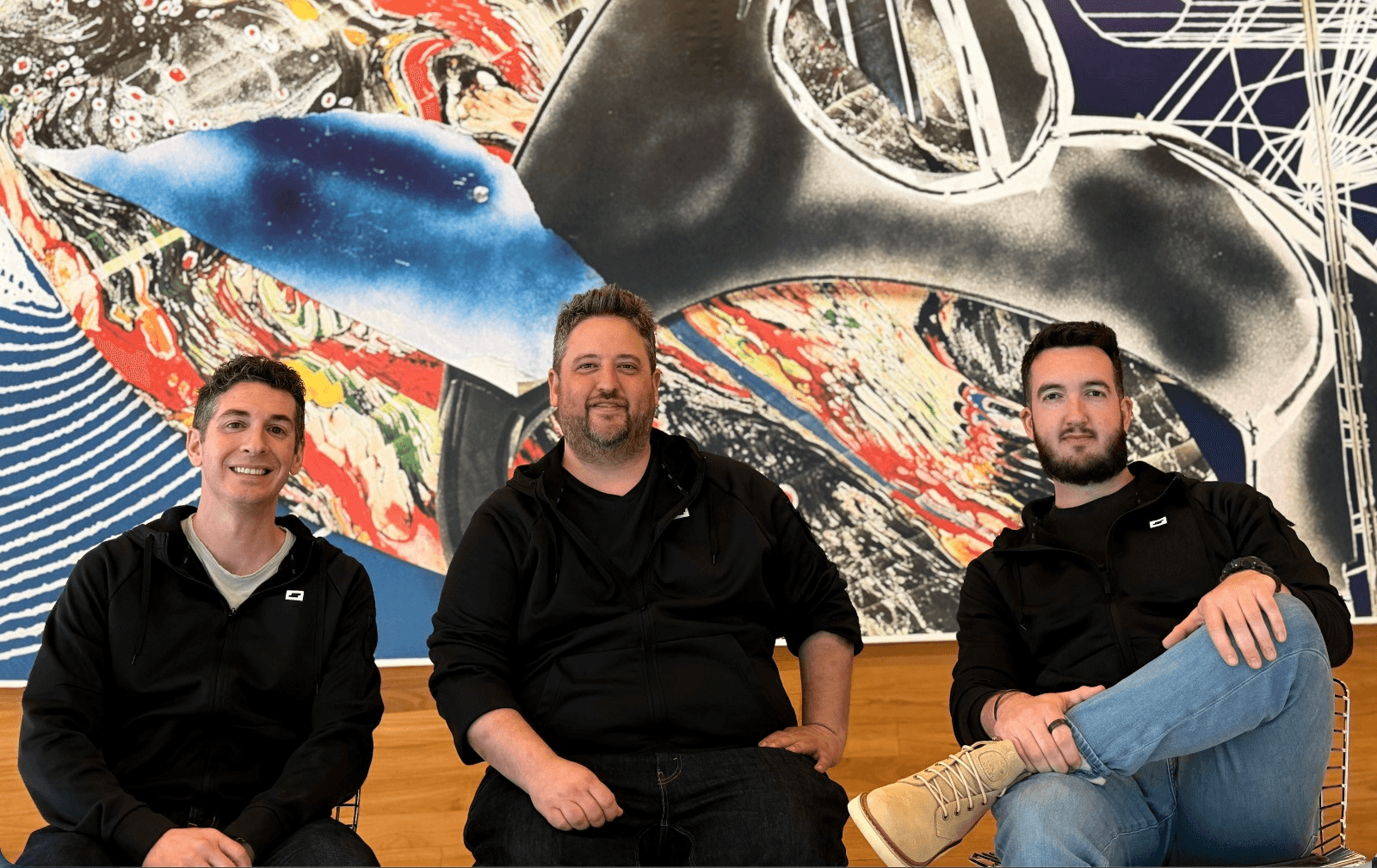
Meny Har is a repeat founder with two exits, including Siemplify, which became Google SecOps. John DiFederico spent seven years building the detection product line inside Exabeam. Dylan Williams has spent the last two years becoming one of the foremost voices on AI-powered detection engineering — building open-source tools, publishing research, and earning credibility in the practitioner community before the company even existed.
Nir Polak and Caleb Sima of Whiterabbit brought this team together. Nir scaled Exabeam over eleven years to a $2.4 billion valuation. Caleb is a three-time founder who has led security at Robinhood, Databricks, and Capital One. They didn't just write a check — they identified the detection engineering problem, validated it across their CISO network, and architected the company alongside Meny, John, and Dylan from the ground up. Shlomo Kramer came in alongside us. When names like these converge on a single seed-stage company, you pay attention.
For us, the signal ran even deeper. Caleb started his career at Internet Security Systems — the same company our partner Tom Noonan founded and built into the undisputed leader in intrusion detection before taking it public and selling to IBM. Dan Ingevaldson, one of the earliest members of X-Force, built his career there too. So did I — writing code for the IPS systems that became the industry standard. I later helped bring QRadar into IBM, the SIEM that defined enterprise detection for a generation.
The founders of commercial intrusion detection. The builders of the SIEM. The CEO who created the behavioral analytics category. A new generation of AI-native detection engineers. Every era of detection is represented at this table — as founders, investors, and board members with skin in the game.
What Comes Next
We've spent our careers inside the detection problem. We built the systems the industry still runs on. And I can see from the inside that the model we helped build — manual rules, human-speed workflows, detection logic written one rule at a time — is now the vulnerability.
What replaces it won't be a faster version of the same manual process. It will be an entirely new substrate — autonomous, continuous, and operating at the speed the threat demands. A detection layer that doesn't wait for a human to write a rule, doesn't degrade when environments change, and doesn't sleep while the adversary iterates. That's what Spectrum is building. That's where this goes.
Machine-speed attacks demand machine-speed detection. Spectrum builds it.
Related
Insights







